Stablecoins have transformed digital finance by offering the speed and flexibility of cryptocurrencies without the volatility typically associated with them. Among them, USDT remains one of the most widely used for trading, payments, remittances, and decentralized finance. However, using USDT safely requires more than just downloading the first wallet you find. Security, control, privacy, and network compatibility all play critical roles in protecting your funds and ensuring smooth transactions.
Creating a secure USDT wallet is not complicated, but it demands careful decisions from the start. The right setup will protect your assets while giving you fast and flexible access across multiple blockchains.
Understanding USDT and Network Compatibility
USDT exists on multiple blockchains, including Ethereum (ERC-20), TRON (TRC-20), Binance Smart Chain (BEP-20), and many others. Each network has different transaction speeds, fees, and ecosystem advantages. Before creating a wallet, it’s essential to understand which network you plan to use most frequently.
If you are transferring USDT between exchanges, speed and low fees may be your priority. If you are using decentralized applications, compatibility with DeFi ecosystems becomes more important. A secure wallet should support multiple blockchains so you are not limited to a single network.
Flexibility matters because blockchain ecosystems evolve rapidly. A wallet that supports 100+ blockchains ensures long-term usability without forcing you to switch platforms later.
Self-Custody vs Custodial Wallets
One of the most important security decisions is choosing between custodial and self-custody wallets. Custodial wallets, often provided by exchanges, hold your private keys on your behalf. While convenient, they expose you to counterparty risk. If the platform is hacked, frozen, or restricted, your funds may become inaccessible.
Self-custody wallets give you full control over your private keys. This means you alone control access to your USDT. The trade-off is responsibility. You must securely store your recovery phrase and protect your device.
For users prioritizing security and independence, self-custody is the stronger choice. It eliminates reliance on third parties and aligns with the core philosophy of decentralized finance.
The Importance of Open-Source Security
Transparency is a critical factor when choosing a crypto wallet. Open-source wallets allow anyone to audit the code, reducing the risk of hidden vulnerabilities or malicious functions. When a wallet’s code is publicly available, it builds trust through verifiability rather than marketing claims.
A fully open-source approach also encourages continuous community review and improvement. This collaborative oversight strengthens security over time and makes it easier to detect potential weaknesses before they become threats.
Security-conscious users often prefer wallets that combine open-source transparency with strong encryption and local key storage.
Choosing the Right Mobile Wallet
Mobile wallets have become the preferred option for many users due to convenience and accessibility. However, convenience should not compromise security. A high-quality mobile wallet should focus on three pillars: security, privacy, and speed. And most importantly, the application must be official and available for free download for AppStore
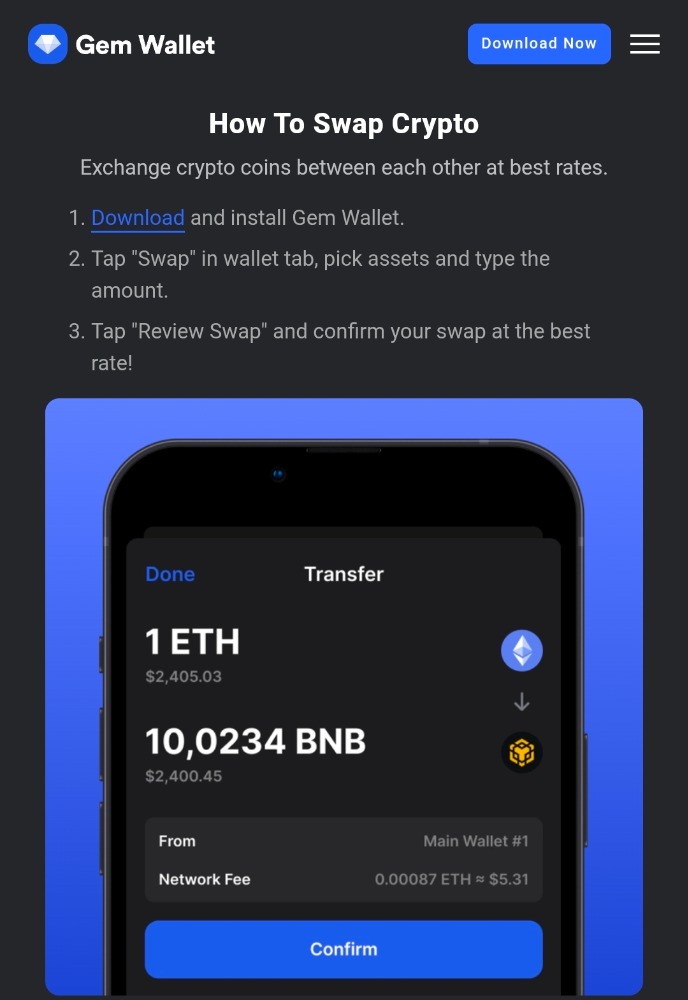
An example of a solution that integrates these priorities is Gem Wallet , a fully open-source, self-custody mobile wallet available on both iOS and Android. Its architecture is designed to give users complete control over private keys while maintaining fast transaction performance across more than 100 supported blockchains. Beyond simple storage, it also allows users to buy, sell, and swap crypto directly within the app, using a built-in DEX aggregator that optimizes trading routes for efficiency.
This combination of multi-chain compatibility, open-source transparency, and built-in exchange functionality reduces the need to move assets between multiple services, lowering exposure to unnecessary risks.
Step-by-Step: Creating a Secure USDT Wallet
The process of creating a secure USDT wallet begins with downloading the application from official sources such as the App Store or Google Play. Verifying authenticity is crucial to avoid malicious clones.
Once installed, the wallet generates a private key and a recovery phrase. This phrase is the master key to your funds. It must be written down offline and stored in a secure location. Avoid screenshots, cloud backups, or digital notes, as these can be compromised.
After securing the recovery phrase, enable additional security features such as biometric authentication or a strong passcode. These measures protect access in case your device is lost or stolen.
When adding USDT to your wallet, select the appropriate network carefully. Sending USDT to the wrong blockchain address can result in permanent loss of funds. Double-check network compatibility before every transaction.
Enhancing Privacy and Control
Privacy in crypto transactions does not mean anonymity by default. Blockchain transactions are publicly recorded, but your personal identity does not need to be directly linked to your wallet address.
A privacy-focused wallet avoids unnecessary data collection and does not require intrusive identity verification for simple storage and transfers. By retaining control over private keys locally on your device, you minimize exposure to centralized databases and third-party tracking.
Maintaining privacy also involves good operational practices. Avoid sharing wallet addresses publicly unless necessary, and consider using separate addresses for different activities.
Fast Transactions Without Compromising Safety
Transaction speed depends largely on the blockchain network you choose. TRC-20 USDT transactions, for example, are typically faster and cheaper than ERC-20 transactions. However, speed should not come at the cost of security.
A well-designed wallet optimizes transaction broadcasting and fee calculation to ensure transfers are processed efficiently. Integrated DEX aggregators further enhance speed by automatically finding optimal liquidity routes when swapping tokens, saving both time and transaction costs.
The ability to manage buying, selling, and swapping within a single secure environment reduces exposure to phishing attacks and fraudulent exchange interfaces.
Multi-Chain Support as a Long-Term Advantage
Supporting 100+ blockchains is not merely a marketing feature; it is a strategic advantage. As new networks emerge and ecosystems evolve, users benefit from flexibility without needing multiple wallets.
Multi-chain support simplifies portfolio management and reduces operational complexity. Instead of managing separate applications for Ethereum, TRON, BNB Chain, and other networks, everything can be accessed within one secure interface.
For active users engaging in DeFi, NFT markets, or cross-chain swaps, this integration saves time while reducing security risks associated with transferring assets between different platforms.
Best Practices for Long-Term Security
Even the most secure wallet cannot protect users from careless habits. Long-term safety depends on discipline and awareness.
Never share your recovery phrase under any circumstances. No legitimate support team will ever ask for it. Regularly update your wallet application to benefit from security patches and improvements. Consider using a dedicated device for large holdings if managing significant funds.
Be cautious when interacting with decentralized applications. Always verify URLs and permissions before connecting your wallet. Phishing remains one of the most common threats in the crypto space.
Final Thoughts
Creating a secure USDT wallet is about more than simply storing stablecoins. It is about maintaining control, ensuring privacy, and enabling fast transactions across multiple networks. Self-custody, open-source transparency, multi-chain support, and integrated exchange functionality are key characteristics to look for.
With the right setup, USDT becomes a powerful tool for global transfers, trading, and decentralized finance participation. By choosing a secure mobile wallet designed with privacy, speed, and transparency at its core, you can confidently manage your stablecoin transactions while minimizing risk.
In the rapidly evolving world of digital assets, security is not optional. It is the foundation upon which every safe and fast transaction is built.